- FortiWeb Interview Questions and Answers [FREQUENTLY ASK]
- 40+ [REAL-TIME] FortiManager Interview Questions and Answers
- ForgeRock Interview Questions and Answers [ TOP & MOST ASKED ]
- [FREQUENTLY ASK] FortiAnalyzer Interview Questions and Answers
- NICE Actimize RPA Interview Questions and Answers [FREQUENTLY ASK]
- Must-Know [LATEST] SonicWall Interview Questions and Answers
- Cisco UCS Interview Questions and Answers [FREQUENTLY ASK]
- Get OKTA Interview Questions and Answers [ TO GET HIRED ]
- Must-Know [LATEST] Cyberoam Interview Questions and Answers
- Get 50+ Fortinet Interview Questions and Answers [FREQUENTLY ASK]
- [30+] Blue Coat Interview Questions and Answers [ FRESHERS ]
- IAM Interview Question and Answers [ TOP & MOST ASKED ]
- Palo Alto Interview Questions and Answers
- Sailpoint Interview Questions and Answers
- Cyberark Interview Questions and Answers
- Cryptography Interview Questions and Answers
- CheckPoint Interview Questions and Answers
- ArcSight Interview Questions and Answers
- Cyber Security Interview Questions and Answers
- Ethical Hacking Interview Questions and Answers
- CCNA Interview Questions and Answers
- FortiWeb Interview Questions and Answers [FREQUENTLY ASK]
- 40+ [REAL-TIME] FortiManager Interview Questions and Answers
- ForgeRock Interview Questions and Answers [ TOP & MOST ASKED ]
- [FREQUENTLY ASK] FortiAnalyzer Interview Questions and Answers
- NICE Actimize RPA Interview Questions and Answers [FREQUENTLY ASK]
- Must-Know [LATEST] SonicWall Interview Questions and Answers
- Cisco UCS Interview Questions and Answers [FREQUENTLY ASK]
- Get OKTA Interview Questions and Answers [ TO GET HIRED ]
- Must-Know [LATEST] Cyberoam Interview Questions and Answers
- Get 50+ Fortinet Interview Questions and Answers [FREQUENTLY ASK]
- [30+] Blue Coat Interview Questions and Answers [ FRESHERS ]
- IAM Interview Question and Answers [ TOP & MOST ASKED ]
- Palo Alto Interview Questions and Answers
- Sailpoint Interview Questions and Answers
- Cyberark Interview Questions and Answers
- Cryptography Interview Questions and Answers
- CheckPoint Interview Questions and Answers
- ArcSight Interview Questions and Answers
- Cyber Security Interview Questions and Answers
- Ethical Hacking Interview Questions and Answers
- CCNA Interview Questions and Answers

40+ [REAL-TIME] FortiManager Interview Questions and Answers
Last updated on 26th Sep 2022, Blog, Cyber Security, Interview Question
1. What purpose will FortiManager solve?
Ans:
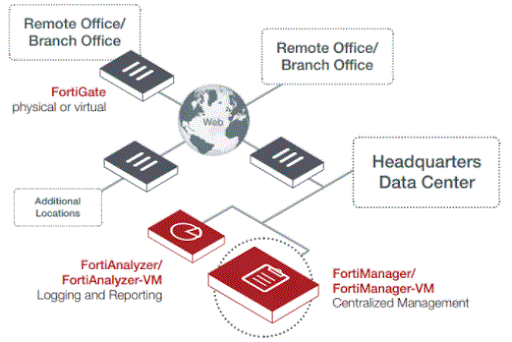
FortiManager is the centralized management console for the Fortinet security framework to manage all of your Fortinet devices. FortiManager appliances enable United States to centrally manage any range of Fortinet devices, from many to thousands, as well as FortiGate, FortiWiFi, FortiCarrier, FortiMail, FortiAnalyzer appliances with virtual appliances, additionally as FortiClient endpoint security agents.
2. However, will we have a tendency to manage our security infrastructure with the assistance of FortiManager?
Ans:
The FortiManager family provides the various wants of network directors for economical management of Fortinet-based security infrastructure. FortiManager minimizes the management prices by a big margin, eases configuration, and accelerates the readying cycles, whether or not deploying new devices, installation of security policies, or distributing updates.
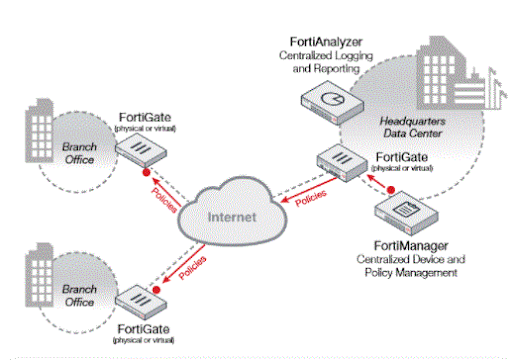
FortiManager offers crucial prompt options like device auto-discovery, cluster management, international policies, auditing facilities, and has the potential to manage advanced VPN environments. FortiManager, as well as the FortiAnalyzer family of centralized work and reportage appliances, provides a whole centralized management resolution for any organization
3. However Fortinet manages its Versatility?
Ans:
Networks want change, because of the evolution of threats, structure growth, or new rules. standard product specialize in mitigating structure threats through firewall policies, code updates, and keeping content security current. FortiManager offers enterprise-class options to contain these threats, however conjointly provides flexibility to evolve at the side of your dynamic network. In addition to having the ability to manage a whole bunch or perhaps thousands of FortiGate devices, FortiManager currently includes basic FortiAnalyzer work and reportage functions for directors preferring a consolidated platform.
4. What’s regionally hosted security content?
Ans:
Hosting security content permits the network administrator for larger management over security content updates associate degreed provides an improved latent period for rating databases. It supports:
- Updates of Antivirus definition.
- Updates within the Intrusion Preventions.
- Updations Vulnerability and Compliance Management.
- Web Filtering & Antispam solely in some chosen systems.
5. What’s the distinction between a Next-Generation Firewall vs. ancient Firewall?
Ans:
NGFWs perform deeper inspections compared to stateful inspections dead by the primary and second-generation firewalls. NGFWs use an additional thorough examination approach, checking packet payloads and matching the signatures for harmful activities like exploitable attacks and malware. NGFWs embrace typical functions of ancient firewalls like packet filtering, network and port address translation (NAT), stateful observation, with virtual personal network (VPN) support. The aim of next-generation firewalls is to incorporate additional layers of the OSI model, up to the filtering of network traffic that’s obsessed with the packet contents.
6. However, will FortiManager perform with FortiAnalyzer?
Ans:
FortiManager Integrated FortiAnalyzer work system permits for tighter integration and correlation of events and policies. A consolidated platform permits network directors straightforward readying of Fortinet management products.
7. What advantages will FortiManager ranked Objects info offer?
Ans:
FortiManager facilitates the utilization of common configurations across the organization in each native and international ADOM levels.
8. What’s machine-controlled Device Provisioning?
Ans:
FortiManager’s machine-controlled Device Provisioning reduces the value of the latest FortiGate for FortiClient installations and maintains policies across all managed assets.
9. However, do body Domains (ADOM) facilitate us?
Ans:
FortiManager permits a network administrator to make teams of devices for alternative directors to observe and manage the following:
- Multiple FortiGate virtual domains (VDOMs) is separated among multiple ADOMs.
- Granular permissions allow distribution of ADOMs and policies to specific users.
- Network directors will solely access devices or VDOMs assigned to them.
- Generate device configuration templates for fast configuration of a replacement Fortinet appliance.
- Within every ATOM, there’s a well-recognized info of objects shared by all devices and policy packages which permit users to utilize similar configurations among a bunch of managed assets.
- Global Policy capabilities are obtainable on all the FortiManager hardware models as well as virtual machines.
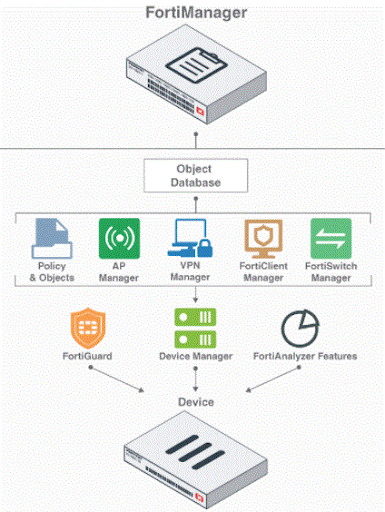
10. What’s FortiManager architecture?
Ans:
11. What’s Command and Management in FortiManager?
Ans:
This facilitate within the Management of devices and end point agents singly or as logical teams
- Automatically discovers the new devices.
- Generates deploys and monitors virtual personal networks.
- Delegate management to alternative users with distributed administration options.
- Audit configuration changes to make sure compliance.
12. However will FortiManager Monitor, Analyze, and Report?
Ans:
- FortiManager accesses very important security and network statistics.
- Monitors period, with integrated basic reportage, providing visibility into network and user activity.
- FortiMnager has additional powerful analytics, combined with the FortiAnalyzer appliance for added data processing and graphical reportage capabilities.
13. What are the FortiManager Supported Devices?
Ans:
Following are the appliances that are being integrated with FortiManager:
FortiGate and FortiCarrier Consolidated Security Appliances:
FortiAP : Wireless Access Points
FortiMail : Electronic communication Security Systems
FortiWeb : Internet Application Security
FortiAnalyzer : Reportage and Analysis Appliances
Fortiswitch : Shift Platforms
Fortisandbox : Advanced Threat Protection Appliances
14. What’s Single Pane-of-Glass Management?
Ans:
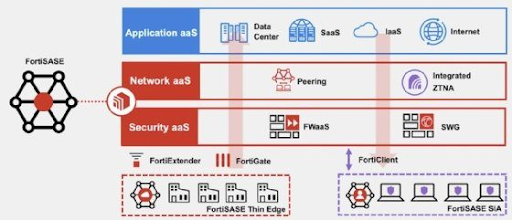
Fortinet Security cloth, legendary for unified, end-to-end protection, is thought of as the Single Pane of Glass. Deploying Fortigate-based security infrastructure to battle advanced threats, and adding FortiManager to produce single-pane-of-glass management across the entire enterprise & providing insights into network-wide traffic and threats.
Forti Manager not solely offers enterprise-class options to attenuate advanced threats however conjointly delivers the industry’s best measurability to manage up to a hundred,000 Fortinet devices.
15. However FortiMnager manages the advancement for audit and compliance?
Ans:
- Automates the method, which reinforces the policy compliance and policy lifecycle management.
- Enforces advancement to attenuate the danger for policy changes
16. What square measures the genus Apis for Automation and Orchestration?
Ans:
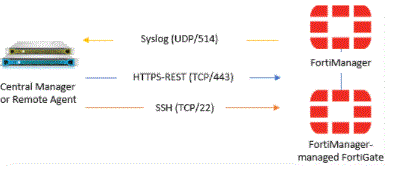
RESTful API permits MSSPs/large enterprises to come up with made-to-order, branded internet portals for policy and object administration automatise common tasks like provisioning new FortiGates and configuring them on existing devices. be part of Fortinet Developer Network (FNDN) to access exclusive articles, a way to move for automation and customization, community-built tools, scripts, and sample code.
17. However is FortiManager’s advancement Mode?
Ans:
Workflow mode is the international model that defines the approval or notification advancement once generating and putting in policy changes. advancement mode, once enabled via command line interface solely, the admin gets a brand new choice within the admin profile page to approve or reject advancement requests.
18. Will we tend to disable the advancement in FortiManager?
Ans:
Yes,we are able to disable the feature. choose the System Settings tab within the navigation pane.
- We should visit System Settings > Dashboard.
- In the command line interface Console contrivance, sort the subsequent command line interface command: config system international
- set workspace-mode disabled
- end
19. What operation will the FortiManager device manager layer provide?
Ans:
- Global ADOM layer
- Adom layer
Device Manager layer contains 2 key pieces: The worldwide object info and every one header and footer policies. Header and footer policies square measure wont to enwrap policies inside every individual ADOM. These square measures are usually invisible to users and devices within the ATOM layer. wherever the FortiManager manages individual devices or teams of devices. it’s within this layer wherever policy packages and folders square measure created, managed, and put in on managed devices.
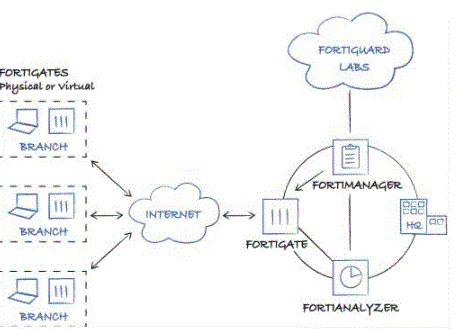
20. Outline FortiManager centralized security management?
Ans:
21. However, will we modify the web-based manager language?
Ans:
We are able to modify the manager to show in English, Simplified Chinese, ancient Chinese, Japanese, or Korean. For best results, you ought to choose the language that the pc software package uses.
We can additionally set the FortiManager Web-based Manager to mechanically find the system language, and by default show the screens within the correct language, if accessible.
22. Will we tend to prohibit Web-based Manager access by the trustworthy host?
Ans:
Preventing unauthorized access to the Web-based Manager is simple. We are able to piece together administrator accounts with trustworthy hosts. Once trustworthy hosts square measure organized, the administrator user will solely log into the Web-based Manager whereas functioning on a laptop with the trustworthy host as outlined within the administrator account. you’ll be able to piece up to 10 trustworthy hosts per administrator account.
23. However, is Fortinet’s Fabric-Ready Partner program completely different from the partner programs we tend to see different vendors promoting?
Ans:
Fortinet’s approach really permits the partners to deliver pre-integrated, end-to-end security offerings prepared for reading in any organization.
24. What’s the most effective way to organize device victimization ADOMs?
Ans:
We can organize devices into ADOMs to permit you to manage these devices. you’ll be able to organize these devices by:
Firmware version: Cluster all devices with a similar computer code version into AN ATOM.
Geographic regions: Cluster all devices for a particular geographic area into AN ATOM, and devices for a special region into another ADOM.
Administrative users: Cluster devices into separate ADOMs supported specific directors answerable for the cluster of devices.
Customers: Cluster all devices for one client into AN ATOM, and devices for one more client into another ATOM.
25. A way to modify the ADOM feature?
Ans:
For sanctioning ADOM feature in FortiManager, we want to:
- Login as admin.
- Go to System Settings > Dashboard.
- In the system info contrivance, choose modify next to body Domain
26. A way to switch between ADOMs?
Ans:
As a network administrator, we tend to square measure able to move between all the ADOMs created on the FortiManager system. This permits the USA to look at, configure, and manage the varied domains. different directors square measure solely able to move between the ADOMs so that they need permission.
They are able to read and administer the domains supporting their account’s permission settings. To access a particular ADOM, we should always choose that ADOM within the tree menu. The FortiManager system presents the accessible choices for that domain, counting on the tab presently in use.
27. A way to manage ADOMs?
Ans:
When the ADOMs feature is enabled, and that we will log in because the admin user, we are able to realize all the accessible ADOMs listed within the tree menu on the various accessible tabs. Within the Policy & Objects tab, a menu bar is offered that permits choosing either international or a particular ADOM from the drop-down list. choosing international or a particular ATOM can then show the policy packages and objects applicable for your choice.
28. Will we have co-occurring ATOM access?
Ans:
System directors will modify or disable co occurring access to a similar ADOM if multiple directors square measure answerable for managing one ATOM. Once enabled, multiple directors will log in to a similar ADOM in parallel.
When disabled, solely one administrator has browse or writes access to the ADOM, whereas all different directors have read-only permission. coincidental ADOM access is enabled or disabled victimization the command line interface
29. What square measures the protection issues, taken under consideration whereas proscribing access to web-based managers?
Ans:
While proscribing access to the FortiManager Web-based Manager we should always check the following:
- We should piece administrator accounts employing a advanced passphrase for native accounts.
- We should piece administrator accounts victimization RADIUS, LDAP, TACACS+, or PKI.
- We should piece the administrator profile to solely permit read/write permission pro re nata and prohibit access victimization read-only or no permission to settings, that aren’t applicable thereto administrator.
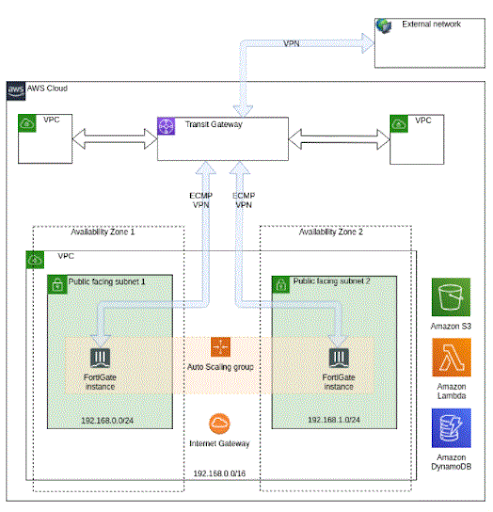
30. What’s the AWS administration guide in FortiManager?
Ans:
31. The way to add ADOM?
Ans:
To add ADOM, we have a tendency to log in as admin. Before that, we have a tendency to change body domains within the Web-based Manager.
32.The way to produce an associate degree ATOM?
Ans:
Either one in every of the subsequent will produce associate degree ATOM.
- Go to the Device Manager tab & opt for Manage ADOMs from the ADOM drop-down list.
- Select produce New within the Manage ADOMs toolbar. instead
- Go to System Settings > All ADOMs and either choose produce New or right-click within the content pane and opt for New from the pop-up menu. The product ADOM panel can open that permits configuring the new ADOM.
33. What will we have a tendency to knock off System Settings?
Ans:
The System Settings tab allows the administrator to manage and assemble the essential system choices for the FortiManager unit. This includes the essential network settings to attach the device to the most network, the configuration of directors and their access permissions, managing and change code for the device
34. Will we have a tendency to customize the dashboard?
Ans:
The FortiManager system dashboard is bespoke simply. We will choose widgets for show, wherever they’re settled on the page, and whether or not they square measure decreased or maximized.
To move a gadget, we should always position your mouse indicator on the widget’s title bar, then click and drag the gadget to its new location.
Dashboard System Settings – to feature a gadget, within the dashboard, choose Add gadget, followed by the names of widgets that we wish to be displayed. to get rid of a gadget we have a tendency to merely shut the icon.
35. However, is RAID managed in FortiManager?
Ans:
RAID helps US to segregate information storage over multiple disks, providing redoubled information responsibility. FortiManager units that contain multiple arduous disks may be RAID designed for capability, performance, and handiness.
We can read the standing of the RAID array from the RAID Management page at System Settings > RAID Management. This page displays the standing of every disk within the RAID array, as well as the system’s RAID level. This gadget conjointly displays what proportion of disc space is employed.
36. Why do we want FortiManager?
Ans:
FortiManager provides granular device and role-based administration for clear visibility of each device and user on the network, facilitating zero-trust, multi-tenancy deployments for giant enterprises and a ranked objects information
37. What’s Adom in FortiManager?
Ans:
A FortiManager body Domain (ADOM) is analogous to the Virtual Domain idea among the FortiGate. {the USe|the utilization|The employment} of ADOMs permits us to form separate logical environments during which we will maintain separate sets of devices.
38. What’s Forti Manager and FortiAnalyzer?
Ans:
FortiManager will add the FortiGates and retrieve configurations for the FortiGates once adding the FortiAnalyzer unit. If FortiAnalyzer is receiving logs from FortiGate devices that don’t exist on FortiManager.
39. However do I hook up with FortiManager?
Ans:
- Connect the FortiManager unit to a management pc victimization associate degree coaxial cable.
- Configure the management pc to get on a similar subnet because the internal interface of the FortiManager unit
- Type admin within the Name field, leave the parole field blank, and click on Login.
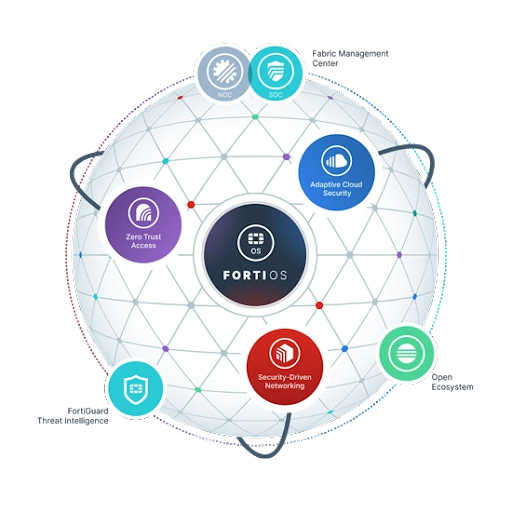
40. What’s FortiManager security fabric?
Ans:
41. What square measures the elemental Of Fortianalyzer?
Ans:
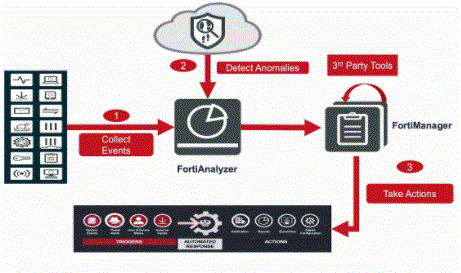
FortiAnalyzer could be a platform that integrates network work, analysis, and coverage right into one machine, delivering accelerated ability of protection occasions at some stage in your network. FortiAnalyzer merchandise decreases the effort needed to scrutinize and maintain policies, additionally to distinguishing attack patterns to help US with great-song structure policies. In quick, FortiAnalyzer affords Centralized work, Analysis, and coverage on a Virtual Platform.
42. However will we have a tendency to Replace arduous Disks?
Ans:
Whenever a tough disk on a FortiAnalyzer unit fails, it’s to be replaced. FortiAnalyzer gadgets that assist hardware RAID, the magnetic disc is also modified at the same time as the FortiAnalyzer unit continues to be going for walks, referred to as hot swapping. On FortiAnalyzer gadgets with software package RAID, the tool needs to be cleaned up prior to commuting the tough disk.
43. The way to assemble Raids?
Ans:
- To assemble the RAID degree we’ve to travel to System Settings > RAID Management.
- Then we should always click on trade beside RAID Level, that displays the RAID Settings spoken communication box.
- We have to decide on a greenhorn raid level from the RAID Level listing, and click on OK.
- The FortiAnalyzer unit can restart itself.
- The period to get the RAID array extensively depends on the chosen RAID level.
44. However will we modify body Access?
Ans:
- To exchange body rights of entry we’ve to 1st visit System Settings > Network.
- By default, port1 settings are also displayed. We will assemble the right of entry for a rare interface.
- We should Click All Interfaces, and choose the interface from the listing.
- We should set the sciencev4 IP Address/Netmask or the IPv6 Address.
- After that we have a tendency to opt for one or further body Access types for the interface, and set the default entryway and name System (DNS) servers among victimization clicking on Apply.
45. However will we have a tendency to Add A Static Route?
Ans:
- After that, we have a tendency to click the Routing Table button to feature associate degree IPv4 static route or the IPv6 Routing Table button to feature associate degree IPv6 static route.
- Then we have a tendency to need to click on the produce New button. The product New Network Route pane is displayed.
- Lastly, we have a tendency to square measure ready to assemble the settings, and click on alright to produce the new static course.
46. What percentage Panes will Fortianalyzer Have And What square measure Its Functions?
Ans:
Banner is on the head of the page; which includes the house button (Fortinet brand), tile menu, ADOM menu (whilst enabled), admin menu, notifications, and assist button.
47. What’s Fetching?
Ans:
We can fetch offline reviews, which might be compressed logs from one FortiAnalyzer unit to a ordinal FortiAnalyzer unit during which the logs which will be robotically indexed within the info to support information analysis on the Log read, FortiView, and Reports tabs. The fetch feature in FortiAnalyzer permits machine administrators to analyze data from compressed logs while not touching the performance of the first FortiAnalyzer unit because of the very fact the strategy of winning logs happens within the history.
48. What’s ancient Storage Provisioning?
Ans:
Storage provisioning is the technique of assignment storage, unremarkably among the form of server disk pressure house, on the thanks to optimize the performance of a garage region network (SAN). Historically, this has been performed via the SAN administrator, and it should be a tedious manner.
49. What’s Skinny Provisioning?
Ans:
Thin provisioning (TP) could be a procedure of maximizing the performance with that the offered space is employed in storage region networks (SAN). skinny Provisioning capabilities with the help of allocating disk cupboard space during a bendy manner amongst one or two consumers, based mostly entirely on the nominal space needed by each user at any given time.
50. Outline FortiManager appliance?
Ans:
51. What’s Thick Provisioning Eager Zeroed?
Ans:
Thick provisioning eager zeroed could be a VMware provisioning technique, that generates a digital contrivance (VM) disk during a default thick format. Thick provision eager zeroed supports bunch options in conjunction with VMware Fault Tolerance, part of VMware vSphere that’s to supply excessive handiness (HA) for leader code packages.
52. What does one Mean By Thick Provision Lazy Zeroed?
Ans:
Thick provision lazy zeroed is the technique of allocating an area among the garage for a virtual system (VM) disk that makes a digital disk during a default thick layout. The thick provision approach all of {the square measure|the world|the realm} elaborated for the digital disk files reserved for the Virtual Machine is formed.
53. However, will we have a tendency to Edit The Fortianalyzer’s informatics Address?
Ans:
- In the toolbar decide plus > Manage/View merchandise, that opens the read merchandise online page.
- Select the FortiAnalyzer VM serial selection and also the Product Details online page opens.
- Select Edit to exchange the define, partner data, and informatics trot out the precise FortiAnalyzer VM.
- Then the Edit Product information online page opens.
- We currently have to be compelled to get into the new informatics address and opt for Save. There isn’t any prohibit of amount of changing the informatics deal with on a whole assessment license
54. What square measure The Fortianalyzer Supporting Devices?
Ans:
- FortiGate Multi-Threat Security Systems.
- FortiMail Email Security Systems.
- FortiClient Mobile End-Point Security.
- FortiClient computer End-Point Security.
- FortiManager Centralized Management.
- Any Syslog-Compatible Device.
55. What’s a Log Browser?
Ans:
Log Browser helps the U.S. to look at log records or messages from the registered devices. We will simply filter the log documents and messages to dig down and find out specific statistics.
56. What Granular data will we Get With the assistance Of Fortianalyzer?
Ans:
The FortiAnalyzer interface (UI) allows the system administrators to dig deep into security log facts to supply the granular stage of news important to apprehend what’s happening at the whole community. Historical or actual-time statistics allows network administrators to research log and content records, further because the web site guests of the total network. The advanced rhetorical analysis tools allow the network administrator to music person activities to the content material degree.
57. What’s a Vulnerability Scanner?
Ans:
FortiAnalyzer’s enclosed vulnerability scanner identifies vulnerabilities on a variety of servers that embrace a mail server, FTP server or another UNIX operating system or Windows host and produces vulnerability reports for that reason displaying the power weaknesses to assaults that would exist for a particular device.
58. What does one perceive By Content work & information Mining?
Ans:
Log aggregation and archiving is important these days in distinctive safety threats and managing network utilization. In addition to in-intensity analysis, period work, and news, FortiAnalyzer facilitates distinctive content material work of client activities and network web site guests. Activities may be scrutinized real time, archived and later analyzed to keep with the need. Activities could also be tracked person sensible, protocol, source, destination, and lots of others. and also the actual content material changed during a session is to be had. Content work isn’t handiest important on the thanks to implement regulatory mandates beside HIPAA and SOX compliance however really had to implement fascinating use pointers and guard important company belongings and intellectual assets.
59. However, will Forti analyzer disagree with ancient Methods?
Ans:
Threats square measure incessantly evolving among networks, like structure boom or new regulative and industrial enterprise wants. ancient methods cognizance on recording and distinctive community threats through work, analysis and news through the years. FortiAnalyzer presents corporation-magnificence functions to not most effectively notice those threats, however in addition provide flexibility to adapt beside the ever-converting network. FortiAnalyzer will generate significantly made-to-order reviews for structure necessities when aggregating logs during a graded, bed work topology.
60. What’s a deep drive into FortiManager?
Ans:
61. However, will we have the benefit of Fortianalyzer’s Versatile Management Solutions?
Ans:
- Diversity of form factors
- Architectural flexibility
- Highly customizable
- Simple licensing
62. What edges If Fortianalyzer is chosen Standalone, Collector, Or instrument Mode?
Ans:
FortiAnalyzer will be mounted as an individual unit, or optimized for distinctive operations. It depends on the world and the utility that can be needed. Any leader will no longer need all the capabilities and blessings of FortiAnalyzer.
63. What area unit the advantages Of Fortianalyzer Seamless Integration With The Fortinet Products?
Ans:
The close to integration with Fortinet merchandise maximizes its performance and permits FortiAnalyzer sources for economical management from FortiGate or alternative FortiManager person interfaces.
64. What area unit the advantages Of Fortianalyzer Centralized work Of Multiple Record Types?
Ans:
This document is at the side of traffic hobby, device events, viruses, assaults, net filtering events, and electronic communication activities and facts. System administrators will scrutinize the whole network from one single place.
65. However, will we have the benefit of Fortianalyzer’s Performance To upmarket Capacity?
Ans:
FortiAnalyzer circle of relatives models aid thousands of FortiGate and FortiClient agents, and should dynamically scale storage supported retention and compliance necessities.
66. What will The Graphical outline Reports Show?
Ans:
Graphical outline reviews offer targeted occasions, activities, and developments happening on FortiGate and third-birthday party devices at the complete network.
67. However Fortianalyzer Manages data associated with Security Events?
Ans:
We can position time lower back in by suggesting that of putting in a FortiAnalyzer platform into the prevailing protection infrastructure, making one read of the safety events, archived content, and vulnerability checks. FortiAnalyzer structures pull the full variety of facts from Fortinet solutions, as well as guests, event, virus, attack, content material filtering, and e-mail filtering. It eliminates the guide search of one or two of log documents while showing rhetorical analysis and community auditing. FortiAnalyzer platform’s centralized statistics archiving, report quarantine and vulnerability analysis additionally reduce the time taken to regulate the vary.
68. What issue Depends On choosing Between Hardware And Virtual Appliances?
Ans:
Most of the agencies use abundant but the required hardware IT infrastructure or virtual IT infrastructure recently, for uncountable value vary constraints. This creates a requirement for each hardware and virtual appliances inside a security strategy. FortiAnalyzer is also connected to either hardware or digital appliances to match the environment, which contains a mixture of digital and bodily IT infrastructure.
69. What area unit the advantages Of Network Event Correlation Benefits?
Ans:
The part mentioned as occasion correlation plays a key role in incorporated management. Network Event Correlation permits the device administrator to fast become awake to and react to network safety threats throughout the corporate community
70. However, does FortiManager add a device?
Ans:
71. However, Fortianalyzer Enhances The Visibility Inside Its Platforms?
Ans:
FortiAnalyzer provides its offerings like security event analysis, rhetorical studies, reporting, content material archiving, and data mining, malicious document quarantining and vulnerability management to teams of any length from a centralized locality. Its practicality of a centralized assortment of knowledge, correlation, and analysis of the assorted written account and geographical safety data from Fortinet appliances & third-celebration devices deliver a simplified, consolidated read of firms danger promotion.
72. What area unit the various authentication and cryptography mechanisms on the market in Fortigate Firewall?
Ans:
- WEP 128 (26 hex digit key).
- WEP sixty four (10 hex digit key).
- None.
- It is wise to use WPA2, that is that the strongest technique for authentication and cryptography.
73. Mention some points whereas configuring the network?
Ans:
Prepare a network diagram consisting of information processing addressing, cabling, and network devices.
74. What’s the command to power off the FortiGate unit via CLI?
Ans:
- To power off the FortiGate unit.
- Execute ending.
75. What area unit the points that ought to be thought of whereas installing/mounting a Fortinet firewall (hardware) within the rack?
Ans:
Below area unit the points of thought whereas mounting a firewall:
- The room temperature ought to be within the vary of close temperature outlined by the first instrumentality Manufacturer (OEM).
- Reliable fastening mechanism.
- Adequate flowing provided for safe operation.
- Adequate precautions for overcurrent and provide wiring.
76. What’s Security Fabric?
Ans:
Security material may be a security resolution to find, monitor, block, and rectify cyber-attacks.
77. What area unit the steps that ought to take before every upgrade of code of the Fortinet firewall?
Ans:
Step 1:Make a copy and store previous configuration.
Step 2: A replica|keep a copy} a copy of the previous code feasible. This can be for the worst-case state of affairs. If something unhealthy happens, you have the associated possibility of rollback.
Step 3: scan the NOTE free by the manufacturer.
Step 4: Upgrade.
78. Describe the steps for backing up the FortiGate configuration via GUI.
Ans:
Dashboard -> choose Backup in System data contrivance -> choose drive for storing -> cypher configuration file – > Enter a watchword and choose Backup – > save the configuration file.
79. What’s the backup configuration file format within the Fortinet firewall?
Ans:
The configuration file can have a .conf extension.
80. What’s Forti Manager and use cases for it?
Ans:
81. However, does one take a backup of the configuration of a Fortinet firewall?
Ans:
You can use below interface commands for backup configuration:
- execute backup config management-station [
- unset allowaccess
- end
- via GUI:
82. A way to maintain short login timeouts whereas accessing the FortiGate firewall?
Ans:
Below command may be accustomed short the login timeouts:
- config system world
- set admin timeout five
- end
83. However, are you able to send logs to FortiAnalyzer/FortiManager in associate degree encrypted format by mistreatment GUI?
Ans:
84. Write the interface command to disable automobile USB installation?
Ans:
Below is that the interface code snip to disable USB installation:
- config system auto-install
- set auto-install-config disable
- set auto-install-image disable
- end
85. However will Fortinet offer support just in case of any problem sweet-faced by a network administrator?
Ans:
Following choices area unit out there to resolve any issue:
- Knowledge Base
- Fortinet Document Library
- Training & Certification
- Fortinet Video Library
- Discussion Forums
- Contact Support
86. What’s the FGCP cluster?
Ans:
FGCP stands for FortiGate bunch Protocol. It’s a proprietary High availability (HA) resolution provided by Fortinet. Fortigate hour angle resolution consists of a minimum of 2 firewalls organized for top availableness operation.
87. However will we tend to set up FortiOS to show world sturdy encryption?
Ans:
Global sturdy cryptography suggests that to permit solely sturdy ciphers (AES, 3DES) and digest (SHA1) for HTTPS, SSH, and SSL/TLS.
- config sys world
- set strong-crypto modify
- end
88. Write the necessary interface command to disable or deactivate automobile USB installation?
Ans:
The following is that the necessary interface code snip to disable or deactivate USB installation:
- Config system auto-install
- Set auto-install-config disable
- Set auto-install-image-disable
- End.
89. What’s FortiManager 300E?
Ans:
91. A way to take a backup of the Fortinet firewall configuration?
Ans:
Here you’ll follow the given interface commands for the backup configuration:
- Execute backup config management- station
- Execute backup config USD < Filename-backup> []
- For FTP;
- Execute backup config ftp [] [] [].
- For TFTP;
- Execute backup config tftp.
92. What area unit the varied steps that ought to be taken by any user before playing up-gradation of the microcode of the Fortinet security Firewall?
Ans:
- Back up -> Store the recent configuration
- Back up the copy -> Then the recent Fortinet microcode may be dead. this is often one in every of the worst-case situations.
Now the user must browse the NOTE command that is discharged by the manufacturer. this might encompass firewall mechanisms helpful info associated with debugging fixation, and take a look at the performance, etc.Finally upgrade the system.

