- How to learn Ethical Hacking?
- How to become a Ethical Hacker ? Know about the requirements to become one
- Introduction to Cyber Security | A Complete Guide
- Top Reasons to Learn Cyber Security | Everything You Need to Know to Become an Expert
- CyberSecurity Framework | How to Implement | A Definitive Guide with Best Practices [ OverView ]
- The Impact of AI and Machine Learning on Cybersecurity | Everything You Need to Know
- What is Certified Ethical Hacker (CEH) Certification and Why is it Important? [ OverView ]
- Benefits Of ECSA Certification | Everything You Need to Know | Expert’s Top Picks
- Top Most OSINT Tools – Open Source Intelligence | Expert’s Top Picks
- Cyber Security Salary in India : Everything You Need to Know
- What is Computer Security? Free Guide Tutorial & REAL-TIME Examples
- Ethical Hacker Salary and Job Description | Everything You Need to Know
- Hacking Tools and Software | All you need to know [ OverView ]
- What is DES? Free Guide Tutorial & REAL-TIME Examples
- How to Become an Ethical Hacker?
- Which are the Best Network Security Certifications?
- Cybersecurity Consultant Career Path
- The Most Effective Data Encryption Techniques
- Great CISSP Books and Study Guides for the CISSP Certification
- What Is Kerberos?
- Top CISSP Domains
- Cyber Security Career Path
- CISSP Certification Exam Guide 2020
- Top Cyber Security Trends for 2020
- CISSP Exam Online 2020
- Compare and Contrast Physical and Environmental Security Controls
- What is information security architect?
- Certified Information Systems Security Professional (CISSP) Certification
- Top Cyber Security Jobs
- What is CISA Certification?
- What is Threat Modeling?
- Certified Information Security Manager (CISM) Certification
- Information Security Management Principles
- Network Perimeter Security Design
- Things You Must Know About Cyber Security in the Cloud
- What is ECSA?
- Why is Cybersecurity Important?
- Tips to Clear Certified Ethical Hacker (CEH) Exam
- Average Annual Salary of a CISSP Certified Professional
- “How to Become a Cyber Security Engineer? “
- Who is an Ethical Hacker?
- What are the requirements to become Cissp certified?
- The Phases of Ethical Hacking
- What is Ethical Hacking?
- Top Ethical Hacking Certifications
- Hash in Python
- How to learn Ethical Hacking?
- How to become a Ethical Hacker ? Know about the requirements to become one
- Introduction to Cyber Security | A Complete Guide
- Top Reasons to Learn Cyber Security | Everything You Need to Know to Become an Expert
- CyberSecurity Framework | How to Implement | A Definitive Guide with Best Practices [ OverView ]
- The Impact of AI and Machine Learning on Cybersecurity | Everything You Need to Know
- What is Certified Ethical Hacker (CEH) Certification and Why is it Important? [ OverView ]
- Benefits Of ECSA Certification | Everything You Need to Know | Expert’s Top Picks
- Top Most OSINT Tools – Open Source Intelligence | Expert’s Top Picks
- Cyber Security Salary in India : Everything You Need to Know
- What is Computer Security? Free Guide Tutorial & REAL-TIME Examples
- Ethical Hacker Salary and Job Description | Everything You Need to Know
- Hacking Tools and Software | All you need to know [ OverView ]
- What is DES? Free Guide Tutorial & REAL-TIME Examples
- How to Become an Ethical Hacker?
- Which are the Best Network Security Certifications?
- Cybersecurity Consultant Career Path
- The Most Effective Data Encryption Techniques
- Great CISSP Books and Study Guides for the CISSP Certification
- What Is Kerberos?
- Top CISSP Domains
- Cyber Security Career Path
- CISSP Certification Exam Guide 2020
- Top Cyber Security Trends for 2020
- CISSP Exam Online 2020
- Compare and Contrast Physical and Environmental Security Controls
- What is information security architect?
- Certified Information Systems Security Professional (CISSP) Certification
- Top Cyber Security Jobs
- What is CISA Certification?
- What is Threat Modeling?
- Certified Information Security Manager (CISM) Certification
- Information Security Management Principles
- Network Perimeter Security Design
- Things You Must Know About Cyber Security in the Cloud
- What is ECSA?
- Why is Cybersecurity Important?
- Tips to Clear Certified Ethical Hacker (CEH) Exam
- Average Annual Salary of a CISSP Certified Professional
- “How to Become a Cyber Security Engineer? “
- Who is an Ethical Hacker?
- What are the requirements to become Cissp certified?
- The Phases of Ethical Hacking
- What is Ethical Hacking?
- Top Ethical Hacking Certifications
- Hash in Python

What is information security architect?
Last updated on 10th Oct 2020, Artciles, Blog, Cyber Security
IT Security Architect
A security architect takes on a vital role in an IT department. You’ll design systems, manage employees and help evolve the security needs of the organization. You can rise to this senior-level position once you have garnered extensive experience and credentials in the computer security field.
What is a Security Architect?
A security architect is a senior-level employee who is responsible for designing, building and maintaining the security structures for an organization’s computer system.
Thinking like a malicious hacker helps a security architect become adept at understanding and anticipating the moves and tactics that a hacker might use to try and gain unauthorized access to the computer system. Throughout the process, security architects report their progress to the CISO.
WHAT DOES A SECURITY ARCHITECT DO?
Security architects assess their organizations’ information technology and computer systems, identifying strengths and weaknesses. They conduct penetration tests, risk analyses, and ethical hacks on local area networks, wide area networks, and virtual private networks. They also assess routers, firewalls, and comparable systems to determine efficacy and efficiency.
Security architects think like hackers. They push existing computer and network security systems to their limits. Once security architects identify vulnerabilities in existing systems, they plan and implement architectural changes to boost security structures.
These professionals often develop and implement entirely new security architectures. They blend knowledge of security hardware and software, organizational needs, and cybersecurity risks with organizational policies and industry standards.
As security architects build and maintain security systems and networks, they prepare budgets, oversee expenses, and allocate personnel resources as needed. Security architects provide guidance to information technology (IT) security team members. They also lead IT analysts, security administrators, and security engineers to coordinate effective security protocols.
Security architects also respond to security breaches. When incidents arise, security architects assess causes, damages, and data recovery, preparing thorough reports for their colleagues, managers, and executives. They also implement appropriate changes, updates, and upgrades in response to vulnerabilities and incursions.
STEPS TO BECOME A SECURITY ARCHITECT
Many security architects boast hacker experience. With experience penetrating existing computer and network security systems, former hackers know what to look for when it comes to weaknesses and vulnerabilities. Security architects also gain knowledge of hacking during undergraduate programs in information technology, computer science, or related disciplines. Most employers prefer security architects to hold at least a bachelor’s degree.
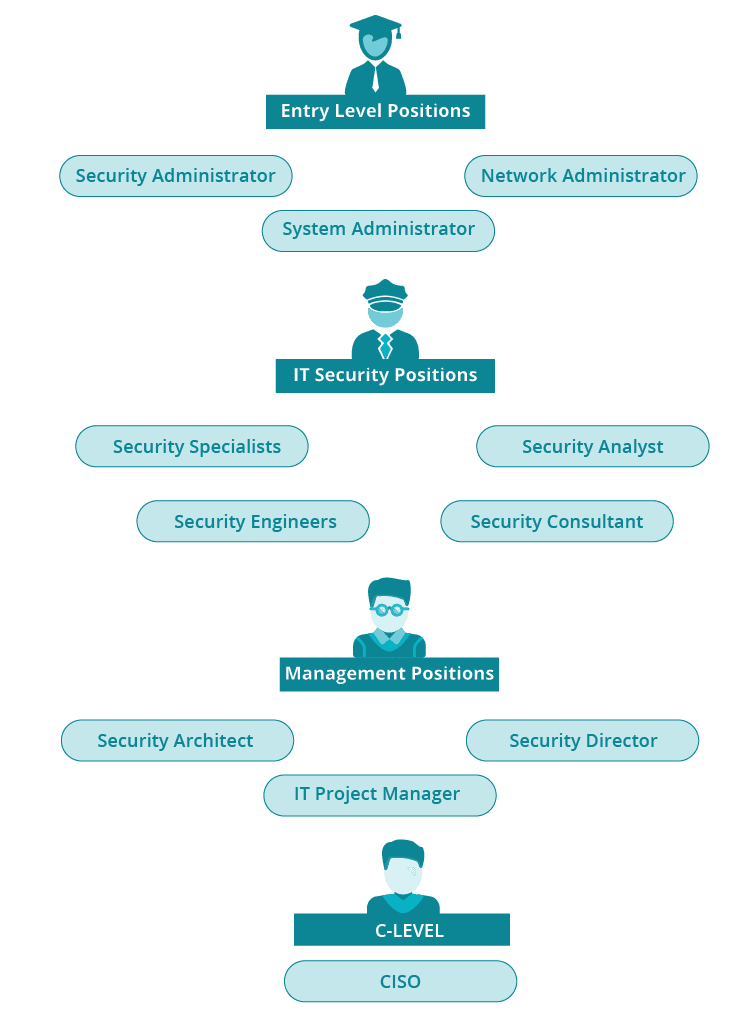
Bachelor’s degrees prepare students to enter the IT profession as security, network, or systems administrators. Security administrators install, administer, and monitor organizations’ security solutions. Network and systems administrators manage organizational information technology infrastructures.
Entry-level experience can lead to mid-level roles as security analysts, engineers, and consultants. Security analysts detect and prevent data incursions, while security engineers design information technology security solutions. The skills developed in entry- and mid-level information technology security positions help professionals move into security architect roles.
Experience remains key in security architecture, but information technology security professionals can earn cybersecurity certifications, as well. Certifications further hone skills, build knowledge, and keep aspiring and practicing security architects current in the field.
(ISC)², a leader in the cybersecurity community, offers an information systems security professional certification. Security architects can earn a specialized CISSP credential in architecture. The program integrates technology, leadership, and analytical content to advance field-specific expertise.
CompTIA offers an advanced security practitioner (CASP+) program, as well. Professionals with CASP+ credentials demonstrate expertise in security domain architectural concepts requirements, plus knowledge of cloud and virtualization technology integration and cryptographic techniques.
Graduate degrees in information technology security, cybersecurity, and comparable areas further enhance security architecture careers. Curricula vary by program, but core classes explore advanced incident handling, ethical hacking, and information security governance. Individuals working in specific industries such as healthcare, finance, or government may further concentrate their degrees.
RESPONSIBILITIES
As a security architect, you’ll be charged with designing security systems to thwart malware, hacker intrusions and Denial of Service attacks. Once the system is in place, you will need to test for any vulnerabilities and audit the entire system. To fully test your system, you may need to hire an outside consultant who can run a thorough penetration test to ensure that the system is secure from outside attacks.

On the managerial side, a security architect may work with other managers to implement employee protocols to maintain system integrity. These protocols are especially pertinent in high-level security situations such as work as a defense contractor. You might implement a policy that states that no workstation should be unattended and that all staff undergo a physical screening upon entering and exiting the department. While seemingly extreme, such measures may be necessary when you are handling data that is vital to national security. As a manager, you will need to implement training for your employees, conduct interviews for new hires, and even let people go when it is necessary.
When new standards and procedures are rolled out, it will fall to you to instruct your staff on these matters. As a management-level employee, you will likely need to stay abreast of current trends in the security field. You will need to travel to conferences and stay abreast of industry publications. Some find it gratifying to publish articles about new security software or best practices for designing a security architecture.
When you are up-to-date on trends in the industry, you will be equipped to assess when and how to upgrade your system. You will then need to oversee the roll out of new software packages, ensuring the integrity of the overall network while you do installations and uninstalls. After such upgrades, you can then perform a new audit to catch any software conflicts or glitches.
SECURITY ARCHITECT VS. SECURITY AUDITOR
Security architects and auditors usually work in the same departments, but the primary distinction between the two is that the architect is often the auditor’s manager. The architect is the one who designs and oversees the roll out of a system, and often the auditor is on the team of staffers who physically implement that roll out.
1.Security Architect: The architect is the one who designs and oversees the roll out of a system.
2.Security Auditor: The auditor is on the team of staffers who physically implement that roll out.
Once the architect’s system is in place, it falls to the auditor to test it and ensure that it is sound. He or she will run tests and scrutinize the results to see if there are any conflicts between various software packages, and determine how to best resolve any conflicts. The architect will review the auditor’s findings and then the two will discuss how to proceed.
Unlike the auditor, an architect will have other managerial duties such as reviewing costs and budgets. You will need to ensure that new software costs are within the budget and that any outside consultants can be paid in a timely fashion. You will often need to be prepared to defend any new expenses to the CEO or CISO of the company. If you are a consultant, it will be vital to discuss budgetary overages with the client so that the firm will be sure to receive payment.
POSSIBLE CAREER PATHS
The road to becoming a security architect likely begins with a bachelor’s degree and proceeds through two tiers in the IT world. If you are interested in pursuing a security career into the management level, you will need to consider at least a graduate-level certificate in computer security, as well as any certificates from industry organizations. This graphic shows the various tiers in your profession:
SIMILAR JOBS
The IT field is full of differing job titles that appear to be very similar jobs. When you are pursuing a position as a security architect, make sure to read and understand the job description and duties so that you are assured that you are applying to the right position. As a security architect, you may be called upon to act as any of the following roles:
- Information Technology Architect
- Information Systems Security Architect
- Enterprise Information Security Architect
SALARIES – ANNUAL MEDIAN SALARY OF $101,210

Security Architect
Computer security is a field that has a high demand for qualified managers, including security and network architects. With such high demand comes high salaries and your years of hard work and service will pay off with a median salary of $101,210 a year, according to the Bureau of Labor Statistics and the job growth for the field is projected at 6 percent through 2026, which is significantly faster than average.
JOB REQUIREMENTS
Most security professionals will begin their career with a bachelor’s degree. While it is preferred that the degree be earned in computer science, information technology or cyber security, you can start with a degree in another field. However, to rise to the level of security architect, you likely need a master’s degree in cyber security or computer science with a security focus. You will need to be knowledgeable in the following topics:
- Windows, Unix and Linux operating systems
- Risk management and assessment procedures
- Security attack pathologies
- Cyber law and ethics
- Network security and architecture
- Wired and wireless security
- Enterprise and security architecture

