- ITIL Tutorial – Incident & amp Problem Management | The BEST Step-By-Step Guide
- ITIL4 Service Value Chain Model Tutorial | Everything You Need to Know
- The ITIL 4 Service Value System | The BEST Step-By-Step Guide
- What are the ITIL 4 Management Practices? | Tutorial for Learning Path
- Guiding Principles of ITIL 4 | Learn Now Tutorial
- Four Dimensions of Service Management in ITIL 4 | A Definitive Guide
- What is the Continual Improvement Model? ITIL Tutorial
- ITIL4 Tutorial | A Complete Guide for Beginners
- Continual Service Improvement (CSI)Tutorial | Learn the Methods and Techniques
- Service Transition Overview – ITIL Tutorial
- ITIL® 4 Foundation Tutorial | The Ultimate Guide
- Design an Effective IT Service with ITIL® v3 Tutorial
- Nagios Tutorial
- ITIL – Service management lifecycle Tutorial
- Service Validation and Testing Tutorial
- Service Operation Processes Tutorial
- ITIL Turtorial
- Services Strategy Tutorial
- ITIL Intermediate SOA – Demand Management Tutorial
- Availability Management Tutorial
- ITIL Key Concepts of the Service Lifecycle Tutorial
- ITIL Change Evaluation Tutorial
- The principles of COBIT® 5 Tutorial
- ITIL Intermediate CSI – Continual Service Improvement Processes Tutorial
- ITIL-Service Level Management Tutorial
- ServiceNow Tutorial
- SCCM Tutorial
- ITIL Tutorial – Incident & amp Problem Management | The BEST Step-By-Step Guide
- ITIL4 Service Value Chain Model Tutorial | Everything You Need to Know
- The ITIL 4 Service Value System | The BEST Step-By-Step Guide
- What are the ITIL 4 Management Practices? | Tutorial for Learning Path
- Guiding Principles of ITIL 4 | Learn Now Tutorial
- Four Dimensions of Service Management in ITIL 4 | A Definitive Guide
- What is the Continual Improvement Model? ITIL Tutorial
- ITIL4 Tutorial | A Complete Guide for Beginners
- Continual Service Improvement (CSI)Tutorial | Learn the Methods and Techniques
- Service Transition Overview – ITIL Tutorial
- ITIL® 4 Foundation Tutorial | The Ultimate Guide
- Design an Effective IT Service with ITIL® v3 Tutorial
- Nagios Tutorial
- ITIL – Service management lifecycle Tutorial
- Service Validation and Testing Tutorial
- Service Operation Processes Tutorial
- ITIL Turtorial
- Services Strategy Tutorial
- ITIL Intermediate SOA – Demand Management Tutorial
- Availability Management Tutorial
- ITIL Key Concepts of the Service Lifecycle Tutorial
- ITIL Change Evaluation Tutorial
- The principles of COBIT® 5 Tutorial
- ITIL Intermediate CSI – Continual Service Improvement Processes Tutorial
- ITIL-Service Level Management Tutorial
- ServiceNow Tutorial
- SCCM Tutorial

Service Operation Processes Tutorial
Last updated on 29th Sep 2020, Blog, IT service and Architecture, Tutorials
Service operation coordinates and carries out the activities and processes required to deliver and manage services at agreed levels to business users and customers. Service operation also manages the technology that is used to deliver and support services.
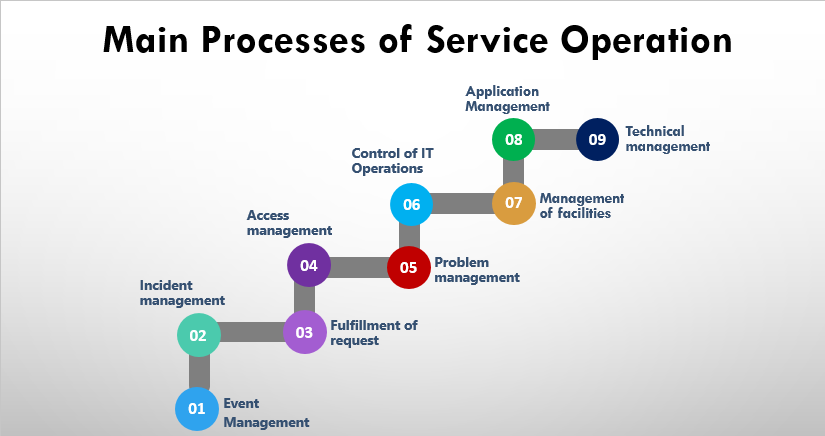
Service operation includes the processes of event management, incident management, request fulfillment, problem management, and access management. Service operation also includes the functions of service desk, technical management, IT operations management, and application management.
Objectives of service operation
- Maintain business satisfaction and confidence in IT through effective and efficient delivery and support of agreed IT services.
- Minimize the impact of service outages on day- to-day business activities.
- Ensure that access to agreed IT services is only provided to those authorized to receive those services.
- Selecting and adopting the best practice as recommended in this publication will assist organizations in delivering significant benefits.
Subscribe For Free Demo
Error: Contact form not found.
Different type of functions in service operation
Strategic objectives are ultimately realized through service operation. ITIL Service Operation provides guidance on how to maintain stability in service operation, allowing for changes in design, scale, scope and service levels.
Organizations are provided with detailed process guidelines, methods and tools for use in two major control perspectives:
- 1. Reactive
- 2. proactive
Reactive vs. Proactive
- Action which takes place when prompted by an external driver is known as Reactive. Proactive is always looking for ways to improve the current situation- Continually looking for potentially impacting changes,can be expensive, better to manage proactively.
- A reactive organization is one which does not act unless it is prompted to do so by an external driver, e.g. a new business requirement. An application that has been developed or escalated in complaints made by users and customers. An unfortunate reality in many organizations is the focus on reactive management mistakenly as the sole means to ensure services that are highly consistent and stable. Actively discouraging proactive behavior from operational staff. The unfortunate irony of this approach is that discouraging effort investment in proactive service management can ultimately increase.
Service Operation Goals
- 1. The purpose of the service operation stage of the service life cycle is to coordinate and carry out. The activities and processes required to deliver and manage services at agreed levels to business users and customers. Service operation is also responsible for the ongoing management of the technology that is used to deliver and support services. It is a critical stage of the service life cycle.
- 2. Well-planned and well-implemented processes will be to no avail if the day-to-day operation of those processes is not properly conducted, controlled and managed. Nor will service improvements be possible if day-to-day activities to monitor performance, assess metrics and gather operational data are not systematically conducted during service operation.
- 3. Staff involved in the service operation stage of the service life cycle should have processes and support tools in place, that allow them to have an overall view of service operation and delivery. Rather than just the separate components, such as hardware, software applications and networks, that make up the end-to-end service from a business perspective.
- 4. These processes and tools should also detect any threats or failures to service quality. As services may be provided, in whole or in part, by one or more partner/supplier organizations, the service operation view of the end-to-end. Service should be extended to encompass external aspects of service provision. When necessary, shared or interfacing processes and tools should be deployed to manage cross-organizational work flows.
Service Operation Processes
Service operations include total five processes as described in the following table −
| Process | Description |
|---|---|
| Event Management | The objective of this process is to make sure all CIs are monitored constantly. It also filters and categorizes the events in order to decide on appropriate actions. |
| Incident Management | The purpose of Incident Management is to restore the service to the previous stage as early as possible. |
| Request Fulfillment | This process deals with handling requests such as changing passwords, creating new users and creating email id etc. |
| Access Management | This process deals with granting rights to authorized users to use the service. |
| Problem Management | This process deals with finding the root cause of the problem and preventing incidents from occurring again. |
Event Management
Purpose
- 1. Purpose to manage events throughout their lifecycle is the purpose of event management. This life cycle of activities to detect events, make sense of them and determine the appropriate control action, which is coordinated by the event management process. Event management is therefore the basis for operational monitoring and control.
- 2. If events are programmed to communicate operational information as well as warnings and exceptions, they can be used as a basis for automating many routine operations management activities.
- Example: Executing scripts on remote devices, or submitting jobs for processing, or even dynamically balancing the demand for a service across multiple devices to enhance performance.
Incident Management
Purpose
- In ITIL terminology, an ‘incident’ is defined as an unplanned interruption to an IT service, or reduction in the quality of an IT service, or a failure of a CI that has not yet impacted an IT service (for example failure of one disk from a mirror set).
- It is the process responsible for managing the life cycle of all incidents. Incidents may be recognized by technical staff, detected and reported by event monitoring tools, communications from users usually via a telephone call to the service desk, or reported by third-party suppliers and partners.
- The purpose of incident management is to restore normal service operation as quickly as possible, and minimize the adverse impact on business operations. Thus, ensuring that agreed levels of service quality are maintained.
- ‘Normal service operation’ is defined as an operational state, where services and CIs are performing within their agreed service and operational levels. Incident management includes any event which disrupts, or which could disrupt, a service. This includes events which are communicated directly by users, either through the service desk or through an interface from event management to incident management tools.
- Incidents can also be reported and/or logged by technical staff. For example, they notice something untoward with a hardware or network component they may report or log an incident and refer it to the service desk).This does not mean, however, that all events are incidents. Many classes of events are not related to disruptions at all, but are indicators of normal operation or are simply informational. Although both incidents and service requests are reported to the service desk, this does not mean that they are the same.
- Service requests do not represent a disruption to agreed service, but are a way of meeting the customer’s needs and may be addressing an agreed target in an SLA. Service requests are dealt with by the request fulfillment process.
Problem Management
Purpose
- Problem management is the process which is responsible to manage the lifecycle of all problems. ITIL defines a ‘problem’ as an underlying cause of one or more incidents. The purpose of problem management is to manage the lifecycle of all problems from first identification through further investigation, documentation and eventual removal.
- Problem management seeks to minimize the adverse impact of incidents and problems on the business that are caused by underlying errors within the IT Infrastructure and to proactively prevent recurrence of incidents related to these errors. In order to achieve this, problem management seeks to get the root cause of incidents, document and communicate the known errors and initiate actions to improve or correct the situation.
Request Fulfillment
Purpose
- The term ‘service request’ is used as a generic description for many different types of demands that are placed upon the IT organization by the users. Many of these are typically requests for small changes that are low risk, frequently performed, low cost etc.
- E.g, a request to change a password, a request to install an additional software application onto a particular workstation, a request to relocate some items of desktop equipment) or maybe just a request for information.
- Request fulfillment is the process responsible for managing the life cycle of all service requests from the users. It is the process for dealing with service requests, many of them are actually smaller, or low risk. The purpose needed to fulfill a request will vary depending upon exactly what is being requested. Some organizations will be comfortable to let the service requests be handled through their incident management processes.
Access Management
Purpose
- Access management is the process of granting authorized users the right to use a service, while preventing access to non-authorized users. It has also been referred to as rights management or identity management in different organizations.
- The purpose of access management is to provide the right for users to be able to use a service or group of services. It is therefore the execution of policies and actions that are defined in the information security management.
Service Operation Functions
Service Operation comprises of four functions as shown in the following diagram

Service Desk
Service Desk is the first and single point of contact. It plays a vital role in customer satisfaction. It coordinates activities between the end user and IT service provider team. It also owns the logged requests and ensures closure of these requests.
There are four types of Service Desk −
- 1. Central Service Desk : In this, there is only one central Service Desk.
- 2. Local or distributed Service Desk : It is costly but closer to the user. It’s difficult to manage and maintain.
- 3. Virtual Service Desk : It is very costly and results in fast processing.
- 4. Specialized Service Desk : It includes dedicated skilled staff for specific queries.
IT Operation Management
This function is responsible for managing organization’s day-to-day operational activities
Technical Management
Technical Management staff includes technical expertises that are responsible for management of overall IT infrastructure.
Application Management
Application Management is responsible for managing applications and software throughout the lifecycle of the service.
Why do we measure Continual Service Improvement?
It would be easy to find out the areas to measure by knowing the new service level requirement, available funds and IT capabilities. IT capabilities are identified in service design and implemented via service transition. CSI conducts gap analysis to identify the opportunities for improvement. If CSI finds that the available tools and resource are not capable enough or if the cost is non-affordable to deliver the desired data then the measure identified in earlier step needs to be revisited.
Collect the Data
Data is gathered according to the goals and objectives of service operation. In order to have raw and quantitative data, monitoring should be in place. The quality of data is critical and it can be gathered through various means – manual or automatic.
Process the data
Once the data is collected it is important to provide it to the audience in required format. Critical Success Factor (CSF’s) and Key Performance Indicator’s (KPI’s) plays a vital role in processing the data. The raw data is organized and divided according to its categories and operation which makes it easy to process and transform the data into information.
Analyze the data and information
The data which is finally information now is carefully analyzed to find missing gaps and its impact on business. The information is thoroughly evaluated taking into consideration all relevant – internal and external factors that can directly or indirectly impact the data. The information is converted into knowledge or facts.
Challenges of Continual Service Improvement
Present and use the information
The analyzed data is shared with the business stakeholders in a clear and defined manner, presenting them an accurate picture of the results of the improvement plan that is implemented. CSI works closely with senior management and assist them to make strategic decisions and determine the next step to optimize and improve the service.
Implement corrective or remedial activities
As CSI has identified the areas that need a change, solutions and remedial plans are communicated to the management to improve the service. A change, thus implemented for the improvement sets a new baseline and the cycle begins again.
The seven step process is the vital process of CSI. It enables an organizational resource to identify and understand which process and function of their service operations needs major enhancement.
Implementation of CSI
For the application of CSI to services and service management processes. At implementation all four stages of the PDDCA cycle are used. With ongoing improvement, CSI draws check and act stages to monitor, measure, review and implement initiatives.
After these four stages a phase of consolidation prevents the circle from rolling back down the hill as shown in the figure. Our goal in using the Deming cycle or PDCA cycle is steady, ongoing improvement. It is a fundamental tenet of Continual Service Improvement (CSI).
PDCA should be repeated multiple times to implement Continual Service Improvement (CSI). Handling of cultural change is required to implement CSI for improvement. It should be noted that the PDCA cycle is a fundamental part of many quality standards including ISO/IEC 20000.
CSI and Service Lifecycle
- Service strategy establishes policies some principles that provide guidance for the whole service lifecycle. The service portfolio is defined in this lifecycle stage and new or changed services are chartered. During the service design stage of the lifecycle, everything needed to transition and operate the new or changed service is documented in a service design package.
- This lifecycle stage also designs everything needed to create, transition and operate the services, including management information systems and tools, architectures, processes, measurement methods and metrics. The activities of the service transition and service operation stages of the lifecycle a defined during service design.
- Service transition ensures that the requirements of the service strategy, which developed in service design are effectively realized in service operation our controlling the risks of failure and disruption.
- The service operation stage of the service lifecycle carries out the activities and processes required to deliver the agreed services.
- During this stage of the lifecycle, the value defined in the service strategy is realized. Continual Service Improvement (CSI) acts in tandem to the lifecycle stages.
- Who processes, activities, roles, services and technology should be measured and subjected to continual improvement. The strength of the service lifecycle rests upon continual feedback throughout each stage of the lifecycle.
- This feedback ensures that service optimization is managed from business perspective and measured in terms of the value the business drivers from services at any point in time during the service lifecycle.
- At every point in the service lifecycle, the process of monitoring, assessment and feedback between each stage drives decisions about the need for minor course corrections or major service improvement initiatives.
- Adopting appropriate technology to automate the processes and provide management with the information that supports the processes is also important for effective and efficient service management.


