- Cryptography Tutorial: What is Cryptanalysis, RC4, and CrypTool [OverView]
- Best Ethical Hacking Tools & Software for Hackers Tutorial | Ultimate Guide to Learn [UPDATED]
- Splunk Enterprise Security Tutorial | Get all the Reviews, Ratings, and Features
- CyberArk Tutorial | For Beginners [ STEP-IN ]
- Types of Wireless Attacks Tutorial
- CISSP – Asset Security Tutorial
- Information Security Governance Tutorial
- Encryption Techniques Tutorial
- IT Threats And Attacks Tutorial
- CISSP
- CISA – Protection of Information Assets Tutorial
- Security Implications Tutorial
- Information Security Management Tutorial
- WebGoat Tutorial
- Steganography Tutorial
- Actimize Tutorial
- Advanced Ethical Hacking – Burpsuite Tutorial
- Cybersecurity Tutorial
- BIOMETRICS Tutorial
- Ethical Hacking Tutorial
- Cryptography Tutorial: What is Cryptanalysis, RC4, and CrypTool [OverView]
- Best Ethical Hacking Tools & Software for Hackers Tutorial | Ultimate Guide to Learn [UPDATED]
- Splunk Enterprise Security Tutorial | Get all the Reviews, Ratings, and Features
- CyberArk Tutorial | For Beginners [ STEP-IN ]
- Types of Wireless Attacks Tutorial
- CISSP – Asset Security Tutorial
- Information Security Governance Tutorial
- Encryption Techniques Tutorial
- IT Threats And Attacks Tutorial
- CISSP
- CISA – Protection of Information Assets Tutorial
- Security Implications Tutorial
- Information Security Management Tutorial
- WebGoat Tutorial
- Steganography Tutorial
- Actimize Tutorial
- Advanced Ethical Hacking – Burpsuite Tutorial
- Cybersecurity Tutorial
- BIOMETRICS Tutorial
- Ethical Hacking Tutorial

Encryption Techniques Tutorial
Last updated on 10th Oct 2020, Blog, Cyber Security, Tutorials
Encryption is a security method in which information is encoded in such a way that only authorized user can read it. It uses encryption algorithm to generate ciphertext that can only be read if decrypted.Encryption Algorithm is the algorithm that is designed to encode a message or information in a way that only authorized parties can have access to data and data is unreadable by unintended parties. There are two types of Encryption Algorithm like Symmetric-key algorithm also known as a secret key algorithm and Asymmetric key algorithm also called a public key algorithm.
What is Data Encryption in Network Security?
Noted antivirus and endpoint security experts at Kaspersky define encryption as “… the conversion of data from a readable format into an encoded format that can only be read or processed after it’s been decrypted.”
They go on to say that encryption is considered the basic building block of data security, widely used by large organizations, small businesses, and individual consumers. It’s the most straightforward and crucial means of protecting information that passes from endpoints to servers.
Considering the elevated risk of cybercrime today, every person and group that uses the internet should be familiar with and incorporate basic encryption techniques, at the very least.
Subscribe For Free Demo
Error: Contact form not found.
How Does Encryption Work?
A woman wants to send her boyfriend a personal text, so she encrypts it using specialized software that scrambles the data into what appears to be unreadable gibberish. She then sends the message out, and her boyfriend, in turn, uses the correct decryption to translate it.
Thus, what starts out looking like this:
fUfDPzlyJu5LOnkBAf4vxSpQgQZltcz7LWwEtrughon5kSQIkQlZtfxtSTstut
q6gVX4SimlC3A6RDAhhL2FfhfoeimC7sDv9G1Z7pCNzFLp0lgAWWA9ACm8r44RZOBi
O5skw9cBZjZVfgmQ9VpFzSwzLLODhCU7/2THg2iDrW3NGQZfz3SSWviwCe7G
mNIvp5jEkGPCGcla4Fgdp/xuyewPk6NDlBewftLtHJVf
=RZx45
…eventually looks like this:
“I accidentally saw your web browser history. You and I are done.”
Fortunately, the keys do all the actual encryption/decryption work, leaving both people more time to contemplate the smoldering ruins of their relationship in total privacy.
Next, in our learning about effective encryption methods, let us find out why we need encryption.
Why Do We Need Encryption?
If anyone wonders why organizations need to practice encryption, keep these four reasons in mind:
- Authentication. Public key encryption proves that a website’s origin server owns the private key and thus was legitimately assigned an SSL certificate. In a world where so many fraudulent websites exist, this is an important feature.
- Privacy. Encryption guarantees that no one can read messages or access data except the legitimate recipient or data owner. This measure prevents cybercriminals, hackers, internet service providers, spammers, and even government institutions from accessing and reading personal data.
- Regulatory Compliance. Many industries and government departments have rules in place that require organizations that work with users’ personal information to keep that data encrypted. A sampling of regulatory and compliance standards that enforce encryption include HIPAA, PCI-DSS, and the GDPR.
- Security. Encryption helps protect information from data breaches, whether the data is at rest or in transit. For example, even if a corporate-owned device is misplaced or stolen, the data stored on it will most likely be secure if the hard drive is properly encrypted. Encryption also helps protect data against malicious activities like man-in-the-middle attacks, and lets parties communicate without the fear of data leaks.
Types of Encryption
There are two types of encryptions schemes as listed below:
- Symmetric Key encryption
- Public Key encryption
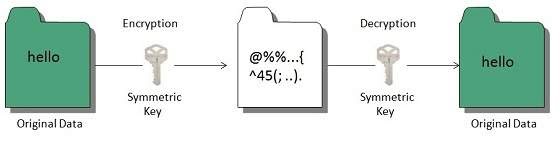
Symmetric Key encryption
Symmetric key encryption algorithm uses same cryptographic keys for both encryption and decryption of cipher text.
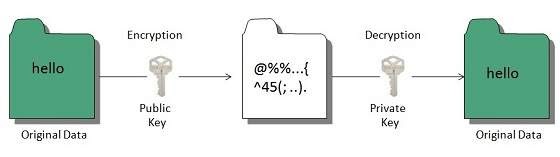
Public Key encryption
Public key encryption algorithm uses pair of keys, one of which is a secret key and one of which is public. These two keys are mathematically linked with each other.
Hashing
In terms of security, hashing is a technique used to encrypt data and generate unpredictable hash values. It is the hash function that generates the hash code, which helps to protect the security of transmission from unauthorized users.
Hash function algorithms
Hashing algorithm provides a way to verify that the message received is the same as the message sent. It can take a plain text message as input and then computes a value based on that message.
Key Points
- The length of computed value is much shorter than the original message.
- It is possible that different plain text messages could generate the same value.
Here we will discuss a sample hashing algorithm in which we will multiply the number of a’s, e’s and h’s in the message and will then add the number of o’s to this value.
For example, the message is “ the combination to the safe is two, seven, thirty-five”. The hash of this message, using our simple hashing algorithm is as follows:
2 x 6 x 3 ) + 4 = 40
The hash of this message is sent to John with cipher text. After he decrypts the message, he computes its hash value using the agreed upon hashing algorithm. If the hash value sent by Bob doesn’t match the hash value of decrypted message, John will know that the message has been altered.
For example, John received a hash value of 17 and decrypted a message Bob has sent as “You are being followed, use backroads, hurry”
He could conclude the message had been altered, this is because the hash value of the message he received is:
(3x4x1)+4 = 16
This is different from then value 17 that Bob sent.
Understanding Symmetric and Asymmetric Algorithm
Let’s discuss the two modes of encryption below:
Symmetric Algorithm
It may be defined as the encryption algorithm that uses a single key to encrypt and decrypt the data. The data has to pass through this algorithm to get transformed into the ciphertext that can be decrypted by any of the peers using the same key that has been used to decrypt it. It is used as the core algorithm to develop other algorithms like Blowfish, Twofish and so on.
Asymmetric Algorithm
It may be defined as the kind of encryption algorithm that uses two different keys to encrypt and decrypt the data. The key used to encrypt the message is called the public key while the key used to decrypt the message is called the private key. Between the two keys, the private key has to be kept very secure to protect the system from a man in the middle attack. The encryption algorithms like RSA uses this mode of encryption.
Encryption Tools and Techniques:
There are few tools available for encryption technique. They include –
- Triple DES – Replaces Data encryption standard(DES) algorithm, uses 3 individual keys with 56 bit.
- RSA – Public encryption algorithm to protect the data over internet. It is an asymmetric key encryption algorithm which uses public and private key.
- Blowfish – It splits the message into 64 bits and encrypts them, is used in certain payment gateways. It is fast, effective and flexible.
- Twofish – Keys in this algorithm are 256 bits in length and it is a symmetric key encryption technique.
- AES – Advanced encryption standard, trusted by many standard organizations. It can encrypt is 128 bit, 192 bit as well as 256-bit.
There are five essential privacy in the internet to be maintained. They are email, file, voice, chat and traffic privacy. Few custom software and applications are available for encryption technique, which includes –
- LastPass – Password manager and used to generate strong and secure passwords.
- BitLocker – Integrated in Windows OS, it is a full disk encryption tool which uses AES for encryption.
- Veracrypt – Similar to Bitlocker, but used in cross platforms like Windows, Linux, OS X and so on.
- DiskCryptor – Free encryption tool, used to even hide system partitions and ISO images.
- HTTPS Everywhere – Makes sure the websites go through an authentication process while connecting to a secure website.
- VPN’s – Tor browser, Express VPN, Cyber ghost and several other tools are available for VPN’s. It is used to ensure that the web traffic and data remains encrypted.
- Using online proxy servers we can hide the IP address and surf anonymously.
Encryption Algorithms
MD5– this is the acronym for Message-Digest 5. It is used to create 128-bit hash values. Theoretically, hashes cannot be reversed into the original plain text. MD5 is used to encrypt passwords as well as check data integrity. MD5 is not collision resistant. Collision resistance is the difficulties in finding two values that produce the same hash values.
- SHA– this is the acronym for Secure Hash Algorithm. SHA algorithms are used to generate condensed representations of a message (message digest). It has various versions such as;
- SHA-0: produces 120-bit hash values. It was withdrawn from use due to significant flaws and replaced by SHA-1.
- SHA-1: produces 160-bit hash values. It is similar to earlier versions of MD5. It has cryptographic weakness and is not recommended for use since the year 2010.
- SHA-2: it has two hash functions namely SHA-256 and SHA-512. SHA-256 uses 32-bit words while SHA-512 uses 64-bit words.
- SHA–3: this algorithm was formally known as Keccak.
- RC4– this algorithm is used to create stream ciphers. It is mostly used in protocols such as Secure Socket Layer (SSL) to encrypt internet communication and Wired Equivalent Privacy (WEP) to secure wireless networks.
- BLOWFISH– this algorithm is used to create keyed, symmetrically blocked ciphers. It can be used to encrypt passwords and other data.
Hacking Activity: Use CrypTool
In this practical scenario, we will create a simple cipher using the RC4 algorithm. We will then attempt to decrypt it using brute-force attack. For this exercise, let us assume that we know the encryption secret key is 24 bits. We will use this information to break the cipher.
We will use CrypTool 1 as our cryptology tool. CrypTool 1 is an open source educational tool for crypto logical studies. You can download it from https://www.cryptool.org/en/ct1-downloads
Creating the RC4 stream cipher
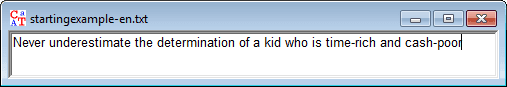
We will encrypt the following phrase
Never underestimate the determination of a kid who is time-rich and cash-poor
We will use 00 00 00 as the encryption key.
- Open CrypTool 1
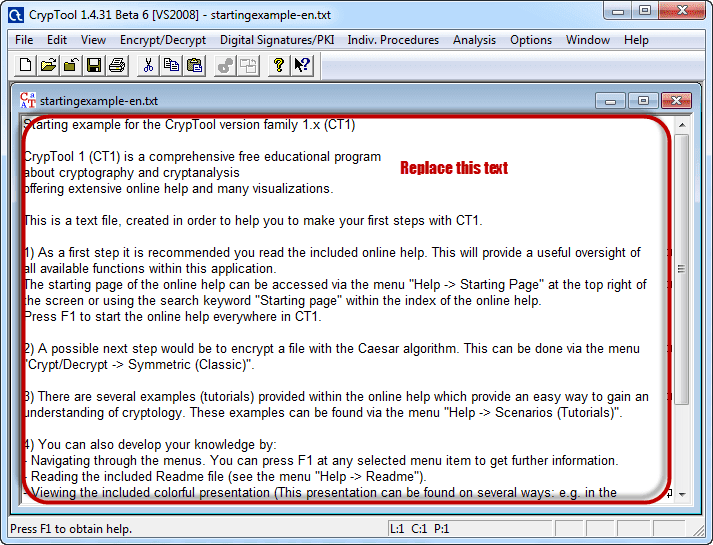
- Replace the text with Never underestimate the determination of a kid who is time-rich and cash-poor
- Click on Encrypt/Decrypt menu
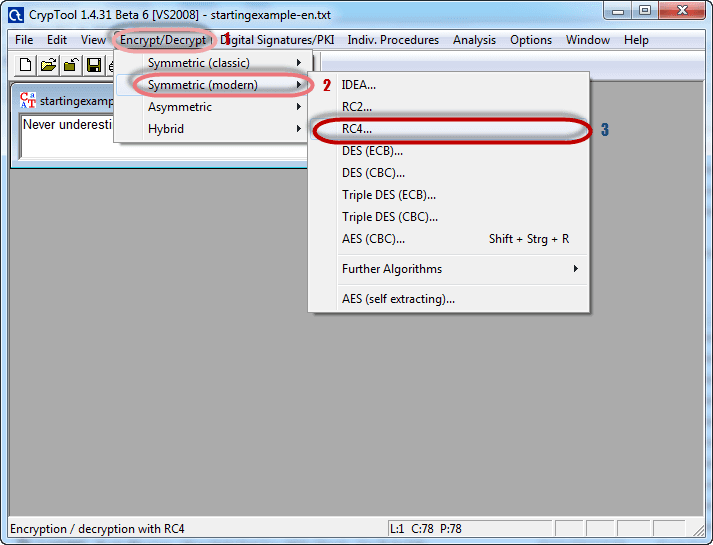
- Point to Symmetric (modern) then select RC4 as shown above
- The following window will appear
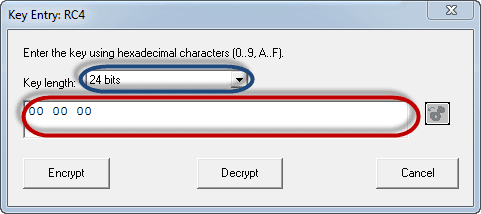
- Select 24 bits as the encryption key
- Set the value to 00 00 00
- Click on Encrypt button
- You will get the following stream cipher

Attacking the stream cipher
- Click on Analysis menu
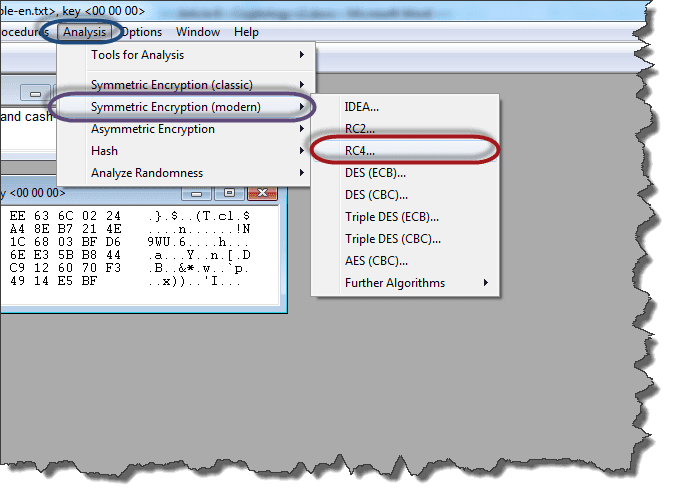
- Point to Symmetric Encryption (modern) then select RC4 as shown above
- You will get the following window
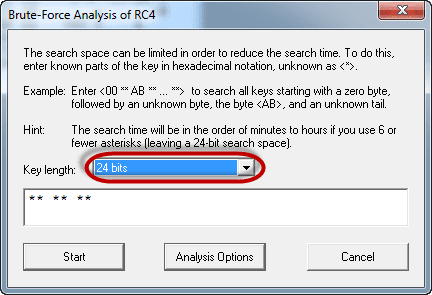
- Remember the assumption made is the secret key is 24 bits. So make sure you select 24 bits as the key length.
- Click on the Start button. You will get the following window

- Note: the time taken to complete the Brute-Force Analysis attack depends on the processing capacity of the machine been used and the key length. The longer the key length, the longer it takes to complete the attack.
- When the analysis is complete, you will get the following results.

- Note: a lower Entropy number means it is the most likely correct result. It is possible a higher than the lowest found Entropy value could be the correct result.
- Select the line that makes the most sense then click on Accept selection button when done
Conclusion
There are several encryption algorithms out there in the market available for us to secure the data that has to be transmitted through the internet. The sole reason for the existence of these algorithms is to protect the man in the middle attack which is concerned with the sniffing of data by someone malicious in an unauthorized manner. Based on the requirement of the software or the hardware system, we can choose the encryption algorithm among various available options. In some organizations, usually, they select any particular algorithm as the standard one in order to transform the message into ciphertext.
As per the requirement based on the speed of encryption, the algorithm has to have opted. For instance, the Blowfish works enough fast to speed up the encryption processes. So many of the systems that require quick encryption and decryption of the data should have to process with Blowfish. When it comes to government-based organizations, they prefer to have their standard encryption algorithm applied everywhere in order to manage the standard. There are several algorithms that have been made available for free so that the organization will low budget in their security department can also leverage it to protect their data being exchanged online.


